With over 20 years of experience in DevSecOps, security, and web development, Timo is a freelance consultant committed to helping clients achieve reliable and secure cloud solutions. Holding CCSP and CEH certifications, Timo possesses vast knowledge secure design and application security programs.
As a DevSecOps architect, Timo collaborates with multiple organizations to design, implement, and monitor best security practices, workflows automation, and integrate security testing tools.
Additionally, Timo provides training and mentorship on security in web applications, both as a freelancer and a university lecturer. Timo’s mission is to empower clients and students with the skills & knowledge to build and maintain secure web applications that meet their customizations.
Projects
Security should to be part of the hole development and operations process. Security related strategic, design and implementation decisions are to be made. As a DevSecOps consultant, I help you introducing and maintaining security into your organizational culture.

Strategic Planning / Intoduction of a Security Culture
Introduction of security into the development lifecycle is a journey and strategic decisions are to be made. I help to make the best strategic cloud- and security decisions. This includes the following programs to scale security
- Security Champions
- Threat Modeling
- Motivation for security for employees at all organizational layers
Assessments
Continuous measurement with OWASP SAMM or my project OWASP DevSecOps Maturity Model provides the ability to plan the next steps.

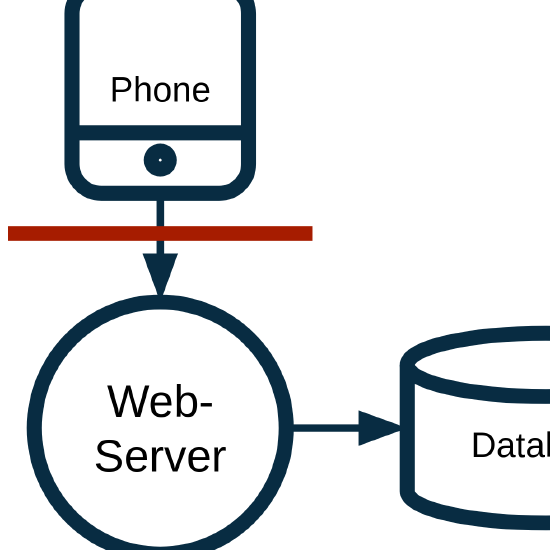
Threat Modeling Program
Threat Modeling is an important part and should be performed as early as possible to reduce the costs fixing security related issues. Depending in the type of the project, different methodologies are used like STRIDE or Cyber Kill Chain.
In addition to performing threat modeling workshops, I am developing threat modeling programs with my clients.

Training / Workshops
Most security frameworks require security related trainings for IT personal. Security aware developers and operators keep security in mind during there regular work leading to much less security issues.
At some clients, I conduct a bi-weekly security training for up to one and a half hour! During this time, we discuss security related organizational issues or innovations and a security related training is provided.

Technical Review
IT systems might become very complex, specially in the cloud environments. Review of the concept and the implementation, e.g. code, is a good way to analyse that security related requirements are met.
DevSecOps
Embrace the full DevSecOps-toolchain and culture to enhance the security of your cloud and applications. We support you to integrate and level up your Application Security Program (AppSec Program)

Trainings

Container Security
Conduction of a container security workshop to show the threats by operating containers.
Agile Threat Modeling
Conduction of a structured analysis to identify threats in IT systems.